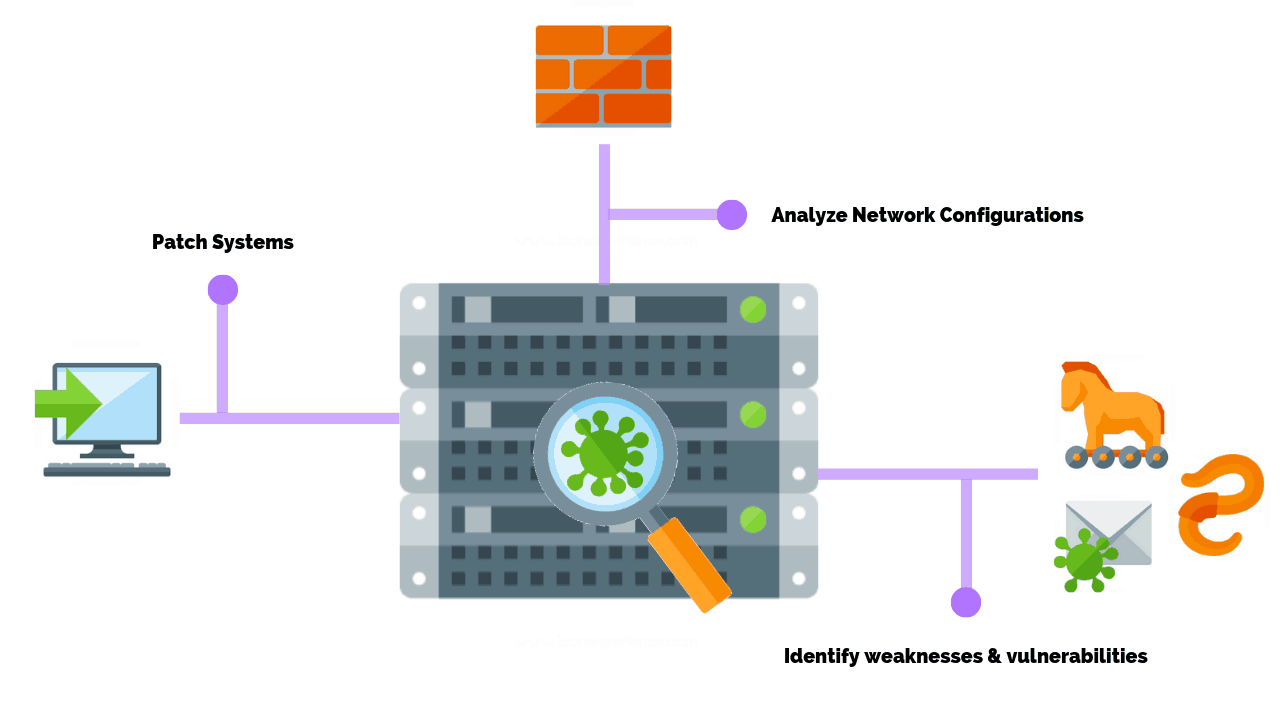
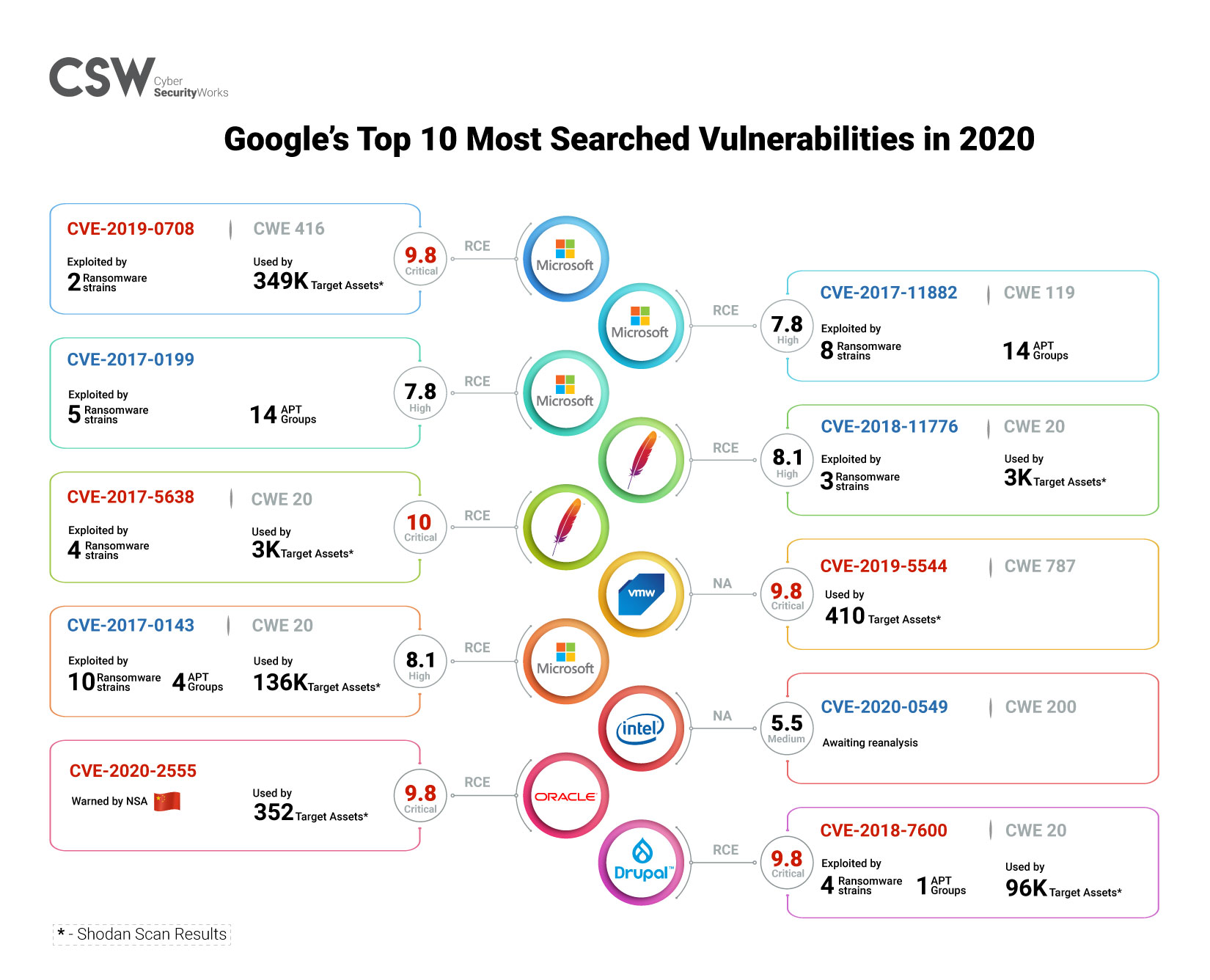
Microsoft's Threat & Vulnerability Management now helps thousands of customers to discover, prioritize, and remediate vulnerabilities in real time - Microsoft Security Blog

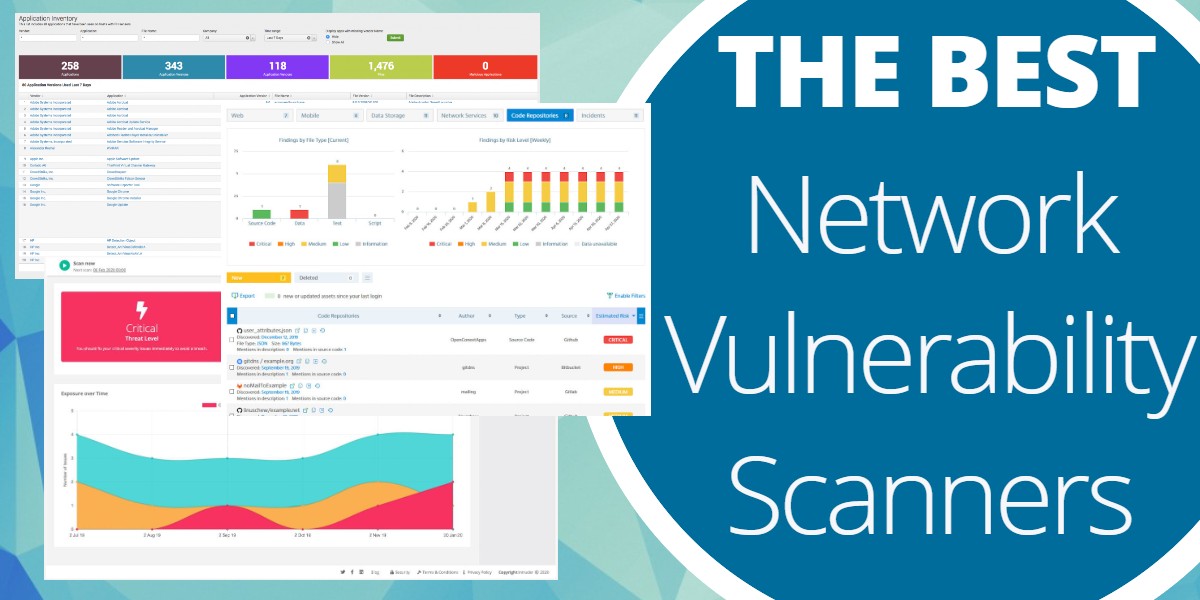
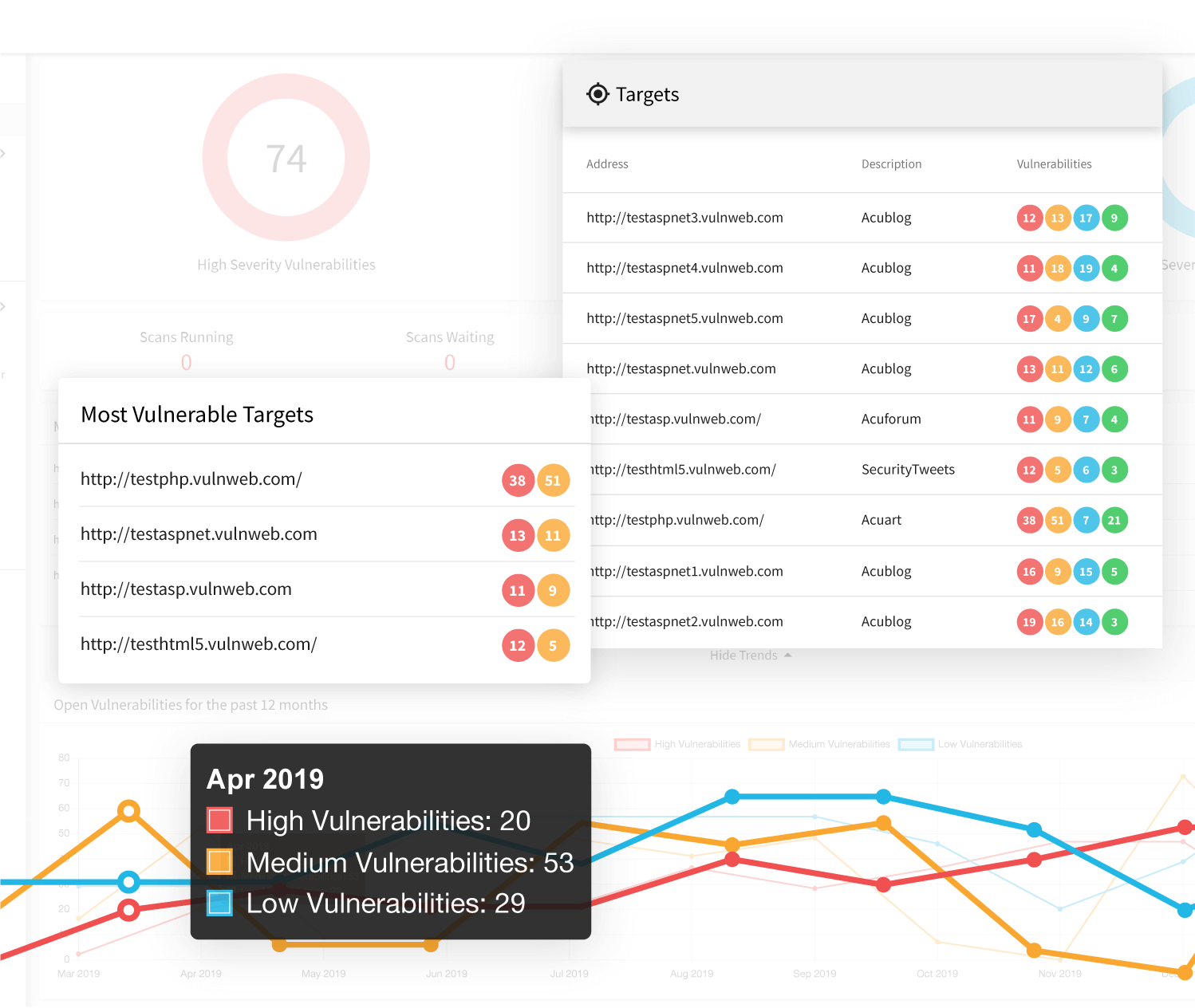
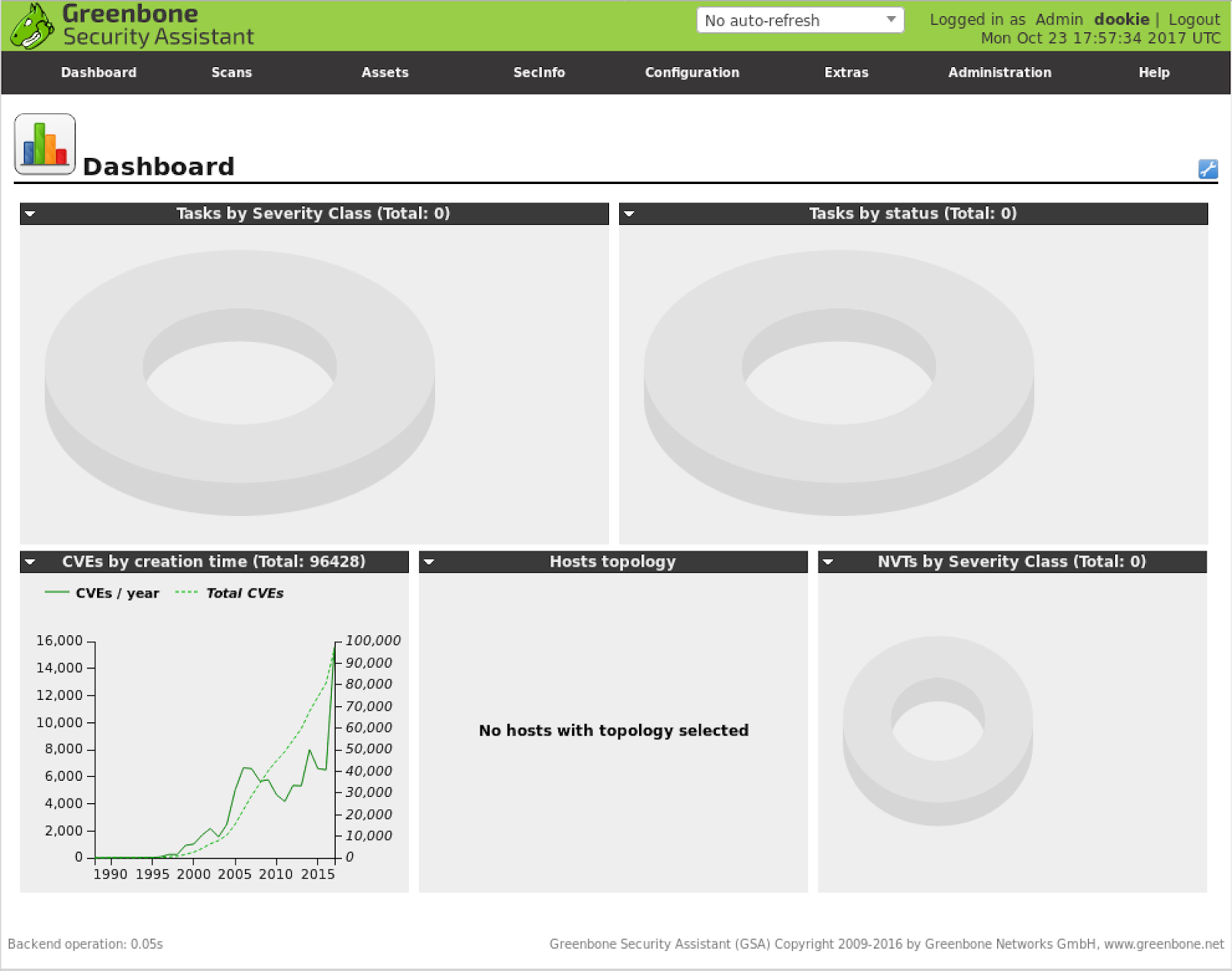
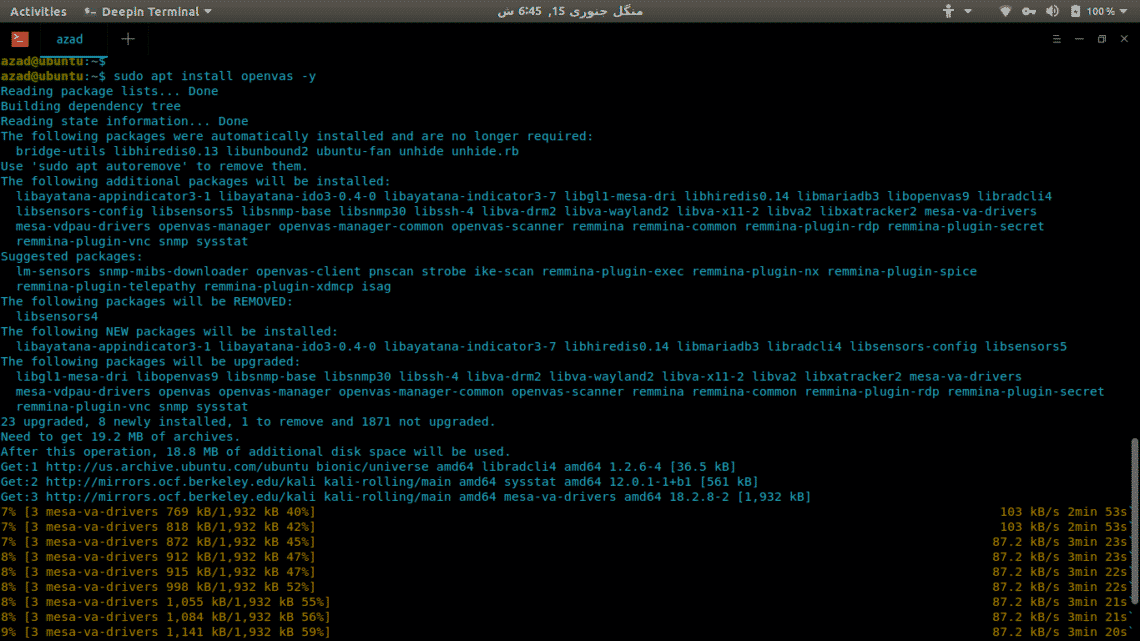
Best Vulnerability Scanners 2019. The article pretends to research about… | by Cybersecurity Manual | Medium